
The Hacker News
Открыть в Telegram
⭐ Official THN Telegram Channel — A trusted, widely read, independent source for breaking news and tech coverage about cybersecurity and hacking. 📨 Contact: admin@thehackernews.com 🌐 Website: https://thehackernews.com
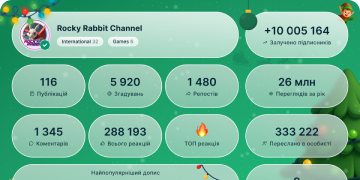
Больше2025 год в цифрах

153 593
Подписчики
+9424 часа
+3767 дней
+1 46330 день
Архив постов
Фото недоступноПоказать в Telegram
North Korea–linked Kimsuky has been tied to a new Android malware campaign.
The group is spreading a fresh DocSwap variant through QR codes on fake CJ Logistics sites. Once installed, the app deploys a full RAT with access to messages, calls, files, audio, and camera.
🔗 Read analysis here → https://thehackernews.com/2025/12/kimsuky-spreads-docswap-android-malware.html
😁 9👍 4🔥 4👏 2
Фото недоступноПоказать в Telegram
A critical ASUS Live Update vulnerability is now on CISA’s exploited list.
CVSS 9.3, supply chain–based, and tied to ShadowHammer, it embedded malicious code in signed updates for carefully chosen devices.
🔗 Read → https://thehackernews.com/2025/12/cisa-flags-critical-asus-live-update.html
🤯 10😁 8👍 5🔥 2
Фото недоступноПоказать в Telegram
🛑 WARNING: CVE-2025-20393 is rated 10.0, with no patch available.
Cisco confirmed active exploitation of an AsyncOS zero-day by a China-linked APT.
The flaw allows root-level command execution on affected email security appliances and enables attackers to establish persistence.
🔗 Details and mitigations → https://thehackernews.com/2025/12/cisco-warns-of-active-attacks.html
😁 18🤯 5🔥 3🤔 3
Фото недоступноПоказать в Telegram
🛑 SonicWall patched an actively exploited flaw in SMA 100 series appliances.
CVE-2025-40602 lets attackers escalate privileges via the management console and was chained with a prior bug for root access.
Patches are now out for affected versions.
🔗 Read → https://thehackernews.com/2025/12/sonicwall-fixes-actively-exploited-cve.html
🔥 6👍 4👏 1
Фото недоступноПоказать в Telegram
🌐 Kimwolf is a new botnet that has infected over 1.8 million Android devices, mainly smart TVs and set-top boxes on home networks.
XLab says it has issued billions of DDoS commands, runs proxy and remote access functions, and uses blockchain-based ENS domains to resist takedowns.
🔗 Read → https://thehackernews.com/2025/12/kimwolf-botnet-hijacks-18-million.html
🔥 7😁 3👍 2
Фото недоступноПоказать в Telegram
⚠️ State-linked APT28 targeted UKR-net with sustained credential harvesting from mid-2024 to 2025.
🕵️♂️ Fake UKR-net login pages hosted on Mocky and relayed via ngrok and Serveo captured credentials and 2FA codes. Phishing PDFs and URL shorteners helped evade filters, showing infrastructure adapted to resist disruption.
🔗 Read campaign details here → https://thehackernews.com/2025/12/apt28-targets-ukrainian-ukr-net-users.html
🔥 10🤯 5😁 2👍 1
Фото недоступноПоказать в Telegram
Kaspersky linked a new phishing wave to Operation ForumTroll.
The Russia-focused APT shifted from organizations to individual academics, using fake eLibrary emails and personalized downloads to deploy a remote-access framework on Windows systems.
🔗 Find how the attack chain worked → https://thehackernews.com/2025/12/new-forumtroll-phishing-attacks-target.html
🔥 6👏 3👍 2
Фото недоступноПоказать в Telegram
Most SOCs still respond after attackers move. That delay costs time and raises breach risk.
ANYRUN says proactive teams use live threat intelligence to see campaigns forming, not just alerts firing. Industry and geo context helps analysts focus on threats that actually matter.
🔗 How SOCs move from reactive to proactive → https://thehackernews.com/2025/12/fix-soc-blind-spots-see-threats-to-your.html
😱 6👍 4🔥 4
Фото недоступноПоказать в Telegram
🛡️ Ink Dragon, a China-aligned hacking group, is focusing on European government targets while staying active in Asia and South America.
It exploits SharePoint and IIS flaws to drop web shells and maintain long-term access using ShadowPad and FINALDRAFT malware.
🔗 Learn more → https://thehackernews.com/2025/12/china-linked-ink-dragon-hacks.html
👍 13🔥 7😁 2😱 2
Фото недоступноПоказать в Telegram
Researchers uncover GhostPoster malware hidden in 17 Firefox add-ons with 50,000+ downloads.
Disguised as VPNs, translators, and ad blockers. 50k+ installs.
JavaScript was hidden inside logo images, activated after days, then hijacked links, tracked browsing, and ran ad fraud.
🔗 Read here → https://thehackernews.com/2025/12/ghostposter-malware-found-in-17-firefox.html
🔥 21🤔 4😁 2
Фото недоступноПоказать в Telegram
🛑 Amazon flagged a new AWS crypto-mining campaign using custom persistence techniques.
Attackers validate permissions with DryRun, deploy miners across ECS and EC2, then enable instance termination protection to block cleanup.
🔗 Learn more: https://thehackernews.com/2025/12/compromised-iam-credentials-power-large.html
🔥 18🤔 7😁 3😱 2
Фото недоступноПоказать в Telegram
💰 A fake NuGet package stole crypto wallets for more than five years.
It copied a popular .NET tracing library and hid as a normal dependency. One extra letter in the author name led to about 2,000 downloads since 2020.
It exfiltrated Stratis wallet JSON files and passwords to a Russian IP.
🔗 Read: https://thehackernews.com/2025/12/rogue-nuget-package-poses-as-tracerfody.html
🤯 12👍 3😁 3🤔 3👏 2🔥 1
00:02
Видео недоступноПоказать в Telegram
⚡ Amazon confirms a Russian GRU unit hacked Western energy and infrastructure networks for years.
The threat wasn’t malware, it was silent credential theft from live traffic.
From 2021–2025, APT44 relied less on zero-days and more on exposed routers and VPN gateways.
🔗 Read → https://thehackernews.com/2025/12/amazon-exposes-years-long-gru-cyber.html
russian.gif.mp40.15 KB
👍 15😁 6🤯 6🔥 4🤔 4
Фото недоступноПоказать в Telegram
⚠️ Most privacy risks aren't malicious.
It’s accidental.
A log statement. A helper function. An AI SDK someone added on Friday.
If you only look in production, you’re blind by design.
Read more → https://thehackernews.com/2025/12/why-data-security-and-privacy-need-to.html
🔥 7👏 3⚡ 2
Фото недоступноПоказать в Telegram
🚨 Fortinet FortiGate devices are under active attack via SSO authentication bypass flaws.
CVE-2025-59718 and CVE-2025-59719 both have CVSS scores of 9.8 and exploit the FortiCloud SSO feature.
Disable FortiCloud SSO until systems are fully updated.
🔗 Details → https://thehackernews.com/2025/12/fortinet-fortigate-under-active-attack.html
😁 14👍 5🤯 5🔥 1
Фото недоступноПоказать в Telegram
Attackers are abusing React2Shell to plant Linux backdoors like KSwapDoor and ZnDoor.
This hits orgs that left React and Next.js servers unpatched.
Microsoft saw reverse shells, Cobalt Strike, and stolen cloud tokens tied to CVE-2025-55182, and Shadowserver tracks over 111,000 exposed IPs.
🔗 Details → https://thehackernews.com/2025/12/react2shell-vulnerability-actively.html
🤯 9😱 5🤔 4🔥 1
Фото недоступноПоказать в Telegram
🔐 Google is shutting down its dark web monitoring tool less than two years after launch.
Google admitted the tool surfaced breached data but didn’t give people clear next steps. Alerts without action paths don’t change outcomes.
🔗 Read here: https://thehackernews.com/2025/12/google-to-shut-down-dark-web-monitoring.html
😁 29🤯 10🔥 5👍 2
Фото недоступноПоказать в Telegram
🚨 WARNING: A “Featured” Chrome extension was silently copying everything users typed into ChatGPT and other AI tools.
Prompts. Responses. Sent off-device by default after an auto-update.
It even warned users about sharing sensitive info, while exporting the full chats itself.
🔗 Read: https://thehackernews.com/2025/12/featured-chrome-browser-extension.html
😁 21🤯 13🔥 12👍 3⚡ 2
Фото недоступноПоказать в Telegram
FreePBX’s worst flaw isn’t a bug — it’s a legacy setting.
If AUTHTYPE is set to webserver, attackers can fake a login header and get admin access. From there, they can add their own user and run code on the system.
Default configs are safe. Old tweaks aren’t.
🔗 Read: https://thehackernews.com/2025/12/freepbx-authentication-bypass-exposed.html
🤯 11😁 6
Фото недоступноПоказать в Telegram
Sensitive data is everywhere: SaaS, cloud, AI pipelines, and most teams can’t see it.
That’s why DSPM is becoming a top security priority for 2026.
Next-gen DSPM goes beyond visibility→ real-time context, automation, and AI-aware protection.
Learn more: https://thn.news/dspm-top-tools
👍 8😁 5
